
|
시장보고서
상품코드
1972226
침투 테스트 시장 : 테스트 유형별, 서비스 유형별, 공격 표면별, 조직 규모별, 전개 방식별, 업계별, 지역별 - 세계 예측(-2031년)Penetration Testing Market by Service Type, Attack Surface - Global Forecast to 2031 |
||||||
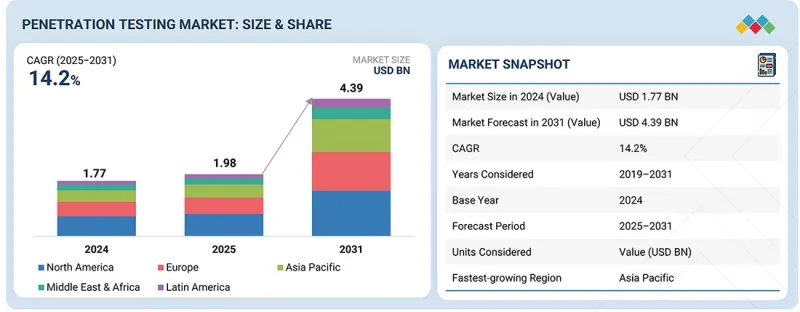
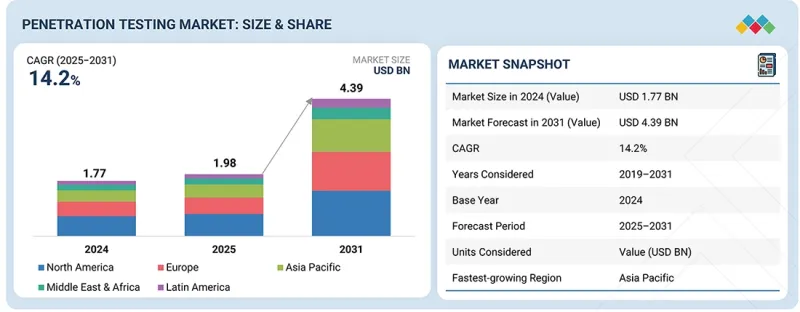
침투 테스트 시장 규모는 예측 기간 동안 CAGR 14.2%로 성장하여 2025년 19억 8,000만 달러에서 2031년에는 43억 9,000만 달러에 달할 것으로 전망됩니다.
전 세계 사이버 보험사의 엄격한 인수 기준은 체계적인 침투 테스트 계약에 대한 수요를 가속화하고 있습니다.
| 조사 범위 | |
|---|---|
| 조사 대상 기간 | 2019-2031년 |
| 기준 연도 | 2024년 |
| 예측 기간 | 2025-2031년 |
| 대상 단위 | 금액(100만/10억 달러) |
| 부문 | 테스트 유형별, 서비스 유형별, 공격 표면별, 조직 규모별, 전개 방식별, 업계별, 지역별 |
| 대상 지역 | 북미, 유럽, 아시아태평양, 중동 및 아프리카, 라틴아메리카 |
보험회사는 보험증권 발행 또는 갱신 조건으로 정기적인 보안 평가 및 리스크 검증에 대한 문서화된 증거를 점점 더 많이 요구하고 있습니다. 그 결과, 기업들은 보상 요건을 충족하고 보험료 인상을 억제하며 적극적인 사이버 리스크 거버넌스를 입증하기 위해 정기적인 침투 테스트 프로그램을 시행하고 있습니다.
중소기업은 업무 및 고객 참여 플랫폼의 디지털화가 진행됨에 따라 적극적인 보안 테스트의 중요성을 점점 더 많이 인식하고 있습니다. 기존에는 제한된 사이버 보안 예산과 내부 전문 지식의 제약이 있었지만, 현재는 웹 애플리케이션, 원격 액세스 시스템, API, 클라우드 워크로드를 타겟으로 하는 위협의 증가에 대응하기 위해 침투 테스트를 우선적으로 수행하고 있습니다. E-Commerce의 확대, SaaS의 도입, 서드파티 통합의 발전으로 공격 표면이 크게 확대되어 랜섬웨어 및 인증정보 기반 공격에 대한 노출 위험이 증가하고 있습니다. 또한, 규제 요건과 대기업 파트너의 공급망 보안에 대한 기대는 중소기업이 체계적이고 감사 가능한 보안 검증 프로그램을 도입하도록 유도하고 있습니다. 이러한 변화로 인해 중소기업의 업무 요구와 리소스 제약에 맞춰 확장성과 비용 효율성이 뛰어난 침투 테스트 서비스 도입이 가속화되고 있습니다.
수동 침투 테스트는 고도의 공격자 기법을 시뮬레이션하고 자동화 툴로는 탐지할 수 없는 미묘한 취약점을 발견할 수 있기 때문에 여전히 주요 서비스 형태입니다. 숙련된 보안 전문가가 애플리케이션, API, 네트워크, 클라우드 환경 전반에 걸쳐 비즈니스 로직 결함, 연쇄 공격 경로, 권한 상승 시나리오, 다단계 악용 기법을 평가합니다. '사이버 보안 보고서 2025'에 따르면, 수동 테스트를 통해 확인된 취약점은 약 2000% 증가했으며, 특히 API, 클라우드 설정, 복잡한 익스플로잇 체인과 같은 고위험 영역에서 두드러지게 나타났습니다. 이러한 영역에서 자동화 도구는 여전히 한계가 있습니다. 보고서는 또한 수동 침투 테스트만으로 약 2,180만 달러의 표적형 위험 노출을 방지할 수 있었다고 지적했습니다. 이러한 결과는 특히 규제 대상 분야에서 심각한 사이버 리스크를 줄이기 위해 심층적인 컨텍스트 검증과 공격자 시뮬레이션이 필수적이라는 점에서 전문가 주도의 평가에 대한 지속적인 의존도를 강조합니다.
중국, 인도, 일본, 호주, 동남아시아 기업들이 디지털 전환을 가속화하고 사이버 보안 프로그램을 강화함에 따라 아시아태평양의 침투 테스트 시장은 빠르게 성장하고 있습니다. 수요는 모바일 및 웹 애플리케이션의 채택 증가, 디지털 결제 시스템의 확대, E-Commerce 플랫폼의 성장, 타사 서비스의 급속한 통합에 의해 주도되고 있습니다. 인도의 데이터 보호법, 중국의 개인정보보호법, 아세안 국가들의 진화하는 사이버 보안 프레임워크와 같은 규제 이니셔티브는 조직이 보안 관리를 검증하고 컴플라이언스를 준수하기 위해 체계적인 침투 테스트를 채택하도록 장려하고 있습니다. 은행, 통신, 정부, 의료 등의 분야의 기업들은 네트워크, 애플리케이션, API, 하이브리드 IT 환경에서 악용될 수 있는 취약점을 탐지하기 위해 자동화된 침투 테스트와 사람이 주도하는 침투 테스트에 모두 투자하고 있습니다. 신흥 디지털 생태계에 대한 악성코드 캠페인과 표적형 공격이 빈번하게 발생하는 이 지역의 다양한 위협 환경은 적극적인 보안 검증과 고도의 공격자 시뮬레이션 활동의 필요성을 더욱 강조하고 있습니다. 아시아태평양 보안 기업과 세계 벤더들의 확장된 에코시스템은 아시아태평양 전체에서 임시 테스트에서 지속적인 침투 테스트 프로그램으로의 전환을 돕고 있습니다.
침투 테스트 시장의 주요 벤더로는 Sophos(영국), Fortra(미국), IBM(미국), Pentera(미국), HackerOne(미국), Invicti(미국), Cobalt(미국), NetSPI(미국), Synack(미국), Bishop Fox(미국), Rapid7(미국), NowSecure(미국), Coalfire(미국), Fortinet(미국), Indium Software(인도), Cigniti Technologies(인도), Raxis(미국), RSI Security(미국), Rhino Security Labs(미국), ScienceSoft(미국), PortSwigger(영국), Netragard(미국), Software Secured(캐나다), Vumetric Cybersecurity(캐나다), Vumetric Cybersecurity(캐나다), Netitude(영국), Zebra(미국) Netitude(영국), Zimperium(미국), SecurityMetrics(미국), Bugcrowd(미국), Cisco(미국), CrowdStrike(미국), LevelBlue(미국), Breachlock(미국), Astra Security(미국), Terra Security(인도), Terra Security(이스라엘) Aikido Security(벨기에).
침투 테스트(Penetration Test) 시장의 주요 기업들에 대한 상세한 경쟁 분석, 기업 프로파일, 최근 동향, 주요 시장 전략 등의 정보를 전해드립니다.
조사 범위
본 보고서에서는 침투 테스트 시장을 다음과 같은 관점에서 세분화하여 시장 규모를 예측하고 있습니다(테스트 유형별, 서비스 유형별, 공격 표면별, 조직 규모별, 전개 방식별, 그리고 산업별).
이 보고서는 주요 시장 플레이어에 대한 상세한 경쟁 분석, 기업 프로파일, 제품 및 사업 제공에 대한 주요 관찰 사항, 최근 동향, 주요 시장 전략에 대해서도 다루고 있습니다.
본 보고서 구매의 주요 이점
이 보고서는 시장 리더와 신규 진입자에게 전체 침투 테스트 시장과 그 하위 부문의 수익 규모에 대한 가장 정확한 추정치를 제공합니다. 이를 통해 이해관계자들은 경쟁 상황을 이해하고, 자사의 포지셔닝을 강화하거나 적절한 시장 진입 전략을 수립하는 데 도움이 되는 귀중한 인사이트를 얻을 수 있습니다. 또한, 시장 동향을 파악하고 주요 시장 촉진요인, 억제요인, 과제, 기회에 대한 정보를 제공합니다.
이 보고서는 다음 사항에 대한 인사이트를 제공합니다:
- 주요 촉진요인(사이버 공격의 빈도와 고도화, DevSecOps 및 CI/CD 파이프라인의 성장) 분석, 억제요인(숙련된 보안 전문가 부족, 높은 침투 테스트 계약 비용) 분석, 기회(자동화 및 AI 기반 침투 테스트 확대, 규제 및 컴플라이언스 요건 강화), 도전 과제(급변하는 공격 기법 및 제로데이 취약점 대응, 자동화 및 심층적인 수동 전문 지식의 균형) 분석 및 컴플라이언스 요건 강화) 분석, 도전과제(빠르게 진화하는 공격 기법 및 제로데이 취약점에 대한 적응, 자동화와 심도 있는 수동 전문 지식의 균형) 분석
- 제품 개발/혁신 : 침투 테스트 시장의 신기술 동향, 연구개발 활동, 신제품 및 서비스 출시에 대한 상세한 분석.
- 시장 개발 : 수익성 높은 시장에 대한 종합적인 정보 - 이 보고서는 다양한 지역의 침투 테스트 시장을 분석합니다.
- 시장 다각화 : 침투 테스트 시장의 신제품 및 서비스, 미개척 지역, 최근 동향, 투자에 대한 종합적인 정보를 제공합니다.
- 경쟁사 평가 : IBM(미국), Sophos(영국), Fortra(미국), NetSPI(미국), Pentera(미국)를 포함한 침투 테스트 시장의 주요 진입업체들의 시장 점유율, 성장 전략, 서비스 제공 내용에 대한 상세한 평가.
자주 묻는 질문
목차
제1장 소개
제2장 주요 요약
제3장 주요 인사이트
제4장 시장 개요
제5장 업계 동향
제6장 기술의 진보, AI에 의한 영향, 특허, 혁신, 그리고 향후 응용
제7장 규제 상황
제8장 소비자 동향과 구매 행동
제9장 침투 테스트 시장(테스트 유형별)
제10장 침투 테스트 시장(서비스 유형별)
제11장 침투 테스트 시장(공격 표면별)
제12장 침투 테스트 시장(조직 규모별)
제13장 침투 테스트 시장(전개 방식별)
제14장 침투 테스트 시장(업계별)
제15장 침투 테스트 시장(지역별)
제16장 경쟁 구도
제17장 기업 개요
제18장 조사 방법
제19장 부록
KSM 26.03.30The penetration testing market is projected to grow from USD 1.98 billion in 2025 to USD 4.39 billion by 2031, at a CAGR of 14.2% during the forecast period. Stricter underwriting standards from global cyber insurance providers are accelerating demand for structured penetration testing engagements.
| Scope of the Report | |
|---|---|
| Years Considered for the Study | 2019-2031 |
| Base Year | 2024 |
| Forecast Period | 2025-2031 |
| Units Considered | Value (USD Million/Billion) |
| Segments | Testing Type, Service Type, Attack Surface, Organization Size, Deployment Mode, and Vertical |
| Regions covered | North America, Europe, Asia Pacific, Middle East & Africa, Latin America |
Insurers increasingly require documented evidence of periodic security assessments and risk validation as a condition for policy issuance or renewal. Consequently, enterprises are implementing recurring penetration testing programs to satisfy coverage requirements, mitigate premium increases, and demonstrate proactive cyber risk governance.
"By organization size, the SMEs segment is expected to witness the highest CAGR during the forecast period."
SMEs are increasingly recognizing the importance of proactive security testing as digital adoption expands across operations and customer engagement platforms. Historically constrained by limited cybersecurity budgets and internal expertise, SMEs are now prioritizing penetration testing to address growing threats targeting web applications, remote access systems, APIs, and cloud workloads. The expansion of e-commerce, SaaS adoption, and third-party integrations has significantly broadened their attack surface, increasing exposure to ransomware and credential-based attacks. In addition, regulatory requirements and supply chain security expectations from larger enterprise partners are pushing SMEs to implement structured and auditable security validation programs. This shift is driving stronger adoption of scalable and cost-effective penetration testing services tailored to SME operational needs and resource constraints.
"By service type, the manual penetration testing segment accounted for the largest market share in 2025."
Manual penetration testing remains the dominant service type due to its ability to simulate sophisticated attacker techniques and uncover nuanced vulnerabilities that automated tools may not detect. Skilled security professionals assess business logic flaws, chained attack paths, privilege escalation scenarios, and multi-step exploitation techniques across applications, APIs, networks, and cloud environments. According to the Cybersecurity Report 2025, there was a nearly 2000% increase in vulnerabilities identified through manual testing, particularly in high-risk areas such as APIs, cloud configurations, and complex exploit chains, where automation still faces limitations. The report also noted that manual penetration testing engagements alone helped prevent approximately USD 21.8 million in targeted risk exposure. These findings underscore the continued reliance on expert-led assessments, especially in regulated sectors where deep contextual validation and adversary simulation are essential to reducing material cyber risk.
"By region, the Asia Pacific is expected to witness the highest CAGR during the forecast period."
The penetration testing market in the Asia Pacific is expanding rapidly as enterprises across China, India, Japan, Australia, and Southeast Asia accelerate digital transformation and strengthen cybersecurity programs. Demand is driven by the increasing adoption of mobile and web applications, the expansion of digital payment systems, the growth of e-commerce platforms, and the rapid integration of third-party services. Regulatory initiatives such as data protection laws in India, the Personal Information Protection Law in China, and evolving cybersecurity frameworks in ASEAN countries are encouraging organizations to adopt structured penetration testing to validate security controls and support compliance. Businesses in sectors such as banking, telecom, government, and healthcare are investing in both automated and human-led penetration testing to detect exploitable vulnerabilities in networks, applications, APIs, and hybrid IT environments. The region's diverse threat landscape, with frequent malware campaigns and targeted attacks against emerging digital ecosystems, is further reinforcing the need for proactive security validation and advanced adversary simulation engagements. A growing ecosystem of regional security firms and global vendors is supporting a shift from ad hoc testing to continuous penetration testing programs across the Asia Pacific.
Breakdown of Primaries
The study draws insights from a range of industry experts, including component suppliers, Tier 1 companies, and OEMs. The break-up of the primaries is as follows:
- By Company Type: Tier 1 - 20%, Tier 2 - 32%, and Tier 3 - 48%
- By Designation: C-level - 40%, Managerial Level, and Others - 60%
- By Region: North America - 40%, Europe - 25%, Asia Pacific - 20%, Middle East & Africa - 10%, and Latin America - 5%
Major vendors in the penetration testing market include Sophos (UK), Fortra (US), IBM (US), Pentera (US), HackerOne (US), Invicti (US), Cobalt (US), NetSPI (US), Synack (US), Bishop Fox (US), Rapid7 (US), NowSecure (US), Coalfire (US), Fortinet (US), Indium Software (India), Cigniti Technologies (India), Raxis (US), RSI Security (US), Rhino Security Labs (US), ScienceSoft (US), PortSwigger (UK), Netragard (US), Software Secured (Canada), Vumetric Cybersecurity (Canada), Netitude (UK), Zimperium (US), SecurityMetrics (US), Bugcrowd (US), Cisco (US), CrowdStrike (US), LevelBlue (US), Breachlock (US), Astra Security (India), Terra Security (Israel), and Aikido Security (Belgium).
The study includes an in-depth competitive analysis of the key players in the penetration testing market, their company profiles, recent developments, and key market strategies.
Research Coverage
The report segments the penetration testing market and forecasts its size based on testing type (black box testing, white box testing, gray box testing), service type (manual penetration testing, automated penetration testing), attack surface (network security penetration testing (internal network testing, external network testing), application security penetration testing (web application penetration testing, mobile application penetration testing, API penetration testing), cloud security penetration testing, social engineering security penetration testing, OT/ICS systems penetration testing), organization size (large enterprises, small and medium enterprises (SMEs)), deployment mode (cloud, on-premises), and vertical (banking, financial services and insurance (BFSI), healthcare, government & public sector, IT & ITeS, telecommunications, manufacturing, retail & ecommerce, energy & utilities, other verticals).
The study also includes an in-depth competitive analysis of the market's key players, their company profiles, key observations related to product and business offerings, recent developments, and key market strategies.
Key Benefits of Buying the Report
The report will help market leaders/new entrants with information on the closest approximations of revenue numbers for the overall penetration testing market and its subsegments. This report will help stakeholders understand the competitive landscape and gain valuable insights to better position their businesses and plan suitable go-to-market strategies. The report also helps stakeholders understand the market pulse and provides information on key market drivers, restraints, challenges, and opportunities.
The report provides insights into the following pointers:
- Analysis of key drivers (rising cyberattack frequency and attack sophistication, growth of DevSecOps and CI/CD pipelines), restraints (shortage of skilled security professionals, high cost of advanced penetration testing engagements), opportunities (expansion of automated and AI-assisted penetration testing, increasing stringency of regulatory and compliance mandates), and challenges (adapting to rapidly evolving attack methods and zero-day exposure, balancing automation with deep manual expertise)
- Product Development/Innovation: Detailed insights on upcoming technologies, research & development activities, and new product & service launches in the penetration testing market.
- Market Development: Comprehensive information about lucrative markets - the report analyses the penetration testing market across varied regions.
- Market Diversification: Exhaustive information about new products & services, untapped geographies, recent developments, and investments in the penetration testing market.
- Competitive Assessment: In-depth assessment of market shares, growth strategies, and service offerings of leading players in the penetration testing market, including IBM (US), Sophos (UK), Fortra (US), NetSPI (US), and Pentera (US).
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 STUDY OBJECTIVES
- 1.2 MARKET DEFINITION
- 1.3 STUDY SCOPE AND SEGMENTATION
- 1.3.1 MARKET SEGMENTATION
- 1.3.2 INCLUSIONS & EXCLUSIONS OF STUDY
- 1.3.3 YEARS CONSIDERED
- 1.3.4 CURRENCY CONSIDERED
- 1.4 STAKEHOLDERS
- 1.5 SUMMARY OF CHANGES
2 EXECUTIVE SUMMARY
- 2.1 MARKET HIGHLIGHTS AND KEY INSIGHTS
- 2.2 KEY MARKET PARTICIPANTS: MAPPING OF STRATEGIC DEVELOPMENTS
- 2.3 DISRUPTIVE TRENDS SHAPING MARKET
- 2.4 HIGH-GROWTH SEGMENTS & EMERGING FRONTIERS
- 2.5 SNAPSHOT: GLOBAL MARKET SIZE, GROWTH RATE, AND FORECAST
3 PREMIUM INSIGHTS
- 3.1 ATTRACTIVE OPPORTUNITIES FOR PLAYERS IN PENETRATION TESTING MARKET
- 3.2 PENETRATION TESTING MARKET, BY SERVICE TYPE
- 3.3 PENETRATION TESTING MARKET, BY ATTACK SURFACE
- 3.4 PENETRATION TESTING MARKET, BY DEPLOYMENT MODE
- 3.5 PENETRATION TESTING MARKET, BY ORGANIZATION SIZE
- 3.6 PENETRATION TESTING MARKET, BY VERTICAL
- 3.7 PENETRATION TESTING MARKET, BY REGION
4 MARKET OVERVIEW
- 4.1 INTRODUCTION
- 4.2 MARKET DYNAMICS
- 4.2.1 DRIVERS
- 4.2.1.1 Rising cyberattack frequency and attack sophistication
- 4.2.1.2 Expanding digital attack surface
- 4.2.1.3 Growth of DevSecOps and CI/CD pipelines
- 4.2.2 RESTRAINTS
- 4.2.2.1 Shortage of skilled security professionals
- 4.2.2.2 High cost of advanced penetration testing engagements
- 4.2.3 OPPORTUNITIES
- 4.2.3.1 Expansion of automated and AI-assisted penetration testing
- 4.2.3.2 Increasing stringency of regulatory and compliance mandates
- 4.2.4 CHALLENGES
- 4.2.4.1 Adapting to rapidly evolving attack methods and zero-day exposure
- 4.2.4.2 Balancing automation with deep manual expertise
- 4.2.1 DRIVERS
- 4.3 UNMET NEEDS AND WHITE SPACES
- 4.4 INTERCONNECTED MARKETS AND CROSS-SECTOR OPPORTUNITIES
- 4.4.1 INTERCONNECTED MARKETS
- 4.4.2 CROSS-SECTOR OPPORTUNITIES
- 4.5 STRATEGIC MOVES BY TIER -1/2/3 PLAYERS
- 4.5.1 CROSS-TIER STRATEGIC PATTERNS
- 4.5.2 STRATEGIC TRENDS
- 4.5.2.1 Cloud-native and PTaaS delivery models
- 4.5.2.2 AI-driven and intelligent simulation workflows
5 INDUSTRY TRENDS
- 5.1 PORTER'S FIVE FORCES ANALYSIS
- 5.1.1 THREAT OF NEW ENTRANTS
- 5.1.2 BARGAINING POWER OF SUPPLIERS
- 5.1.3 BARGAINING POWER OF BUYERS
- 5.1.4 THREAT OF SUBSTITUTES
- 5.1.5 INTENSITY OF COMPETITIVE RIVALRY
- 5.2 MACROECONOMIC INDICATORS
- 5.2.1 INTRODUCTION
- 5.2.2 GDP TRENDS AND FORECAST
- 5.2.3 TRENDS IN GLOBAL ICT INDUSTRY
- 5.2.4 TRENDS IN GLOBAL CYBERSECURITY INDUSTRY
- 5.3 VALUE CHAIN ANALYSIS
- 5.3.1 PENETRATION TESTING MARKET PROVIDERS
- 5.3.2 TECHNOLOGY PROVIDERS
- 5.3.3 CONSULTANTS AND INTEGRATORS
- 5.3.4 REGULATORY BODIES AND STANDARDS
- 5.3.5 CHANNEL PARTNERS (CONSULTATION, DISTRIBUTORS, RESELLERS, & VARS)
- 5.3.6 VERTICALS (END USERS)
- 5.4 ECOSYSTEM ANALYSIS
- 5.5 PRICING ANALYSIS
- 5.5.1 AVERAGE SELLING PRICE TREND OF KEY VENDORS, BY SERVICE TYPE, 2025
- 5.5.2 INDICATIVE PRICING ANALYSIS, BY VENDOR
- 5.6 KEY CONFERENCES & EVENTS, 2026
- 5.7 TRENDS AND DISRUPTIONS IMPACTING CUSTOMER BUSINESS
- 5.8 INVESTMENT AND FUNDING SCENARIO
- 5.9 CASE STUDY ANALYSIS
- 5.9.1 ORGANIZATIONAL PENETRATION TESTING ENABLES COMPLIANCE READINESS FOR GLOBAL OIL AND ENERGY ENTERPRISE
- 5.9.2 AWS PENETRATION TESTING DELIVERS IN-DEPTH CYBER RISK VISIBILITY FOR SPECIALIST BANK
- 5.9.3 SOCIAL ENGINEERING AND PENETRATION TESTING IMPROVES CYBER RESILIENCE FOR US HEALTHCARE PROVIDER
- 5.9.4 PENETRATION TESTING ENHANCE REGULATORY READINESS FOR UK BETTING PLATFORM
- 5.10 IMPACT OF 2025 US TARIFF - PENETRATION TESTING MARKET
- 5.10.1 INTRODUCTION
- 5.10.2 KEY TARIFF RATES
- 5.10.3 PRICE IMPACT ANALYSIS
- 5.10.4 IMPACT ON COUNTRY/REGION
- 5.10.4.1 North America
- 5.10.4.2 Europe
- 5.10.4.3 Asia Pacific
- 5.10.5 IMPACT ON END-USE INDUSTRIES
6 TECHNOLOGICAL ADVANCEMENTS, AI-DRIVEN IMPACT, PATENTS, INNOVATIONS, AND FUTURE APPLICATIONS
- 6.1 TECHNOLOGY ANALYSIS
- 6.1.1 KEY EMERGING TECHNOLOGIES
- 6.1.1.1 Artificial intelligence (AI)
- 6.1.1.2 Breach & attack simulation (BAS)
- 6.1.2 COMPLEMENTARY TECHNOLOGIES
- 6.1.2.1 Secure code review & SAST/DAST tools
- 6.1.2.2 Vulnerability management solutions
- 6.1.3 ADJACENT TECHNOLOGIES
- 6.1.3.1 Continuous security validation/Exposure management platforms
- 6.1.1 KEY EMERGING TECHNOLOGIES
- 6.2 TECHNOLOGY/PRODUCT ROADMAP
- 6.2.1 SHORT-TERM (2026-2027) | FOUNDATION & EARLY COMMERCIALIZATION
- 6.2.2 MID-TERM (2027-2030) SCALING, INTELLIGENCE, & ECOSYSTEM EXPANSION
- 6.2.3 LONG-TERM (2030-2035+) | AUTONOMOUS
- 6.3 PATENT ANALYSIS
- 6.4 FUTURE APPLICATIONS
- 6.4.1 BREACH-READINESS VALIDATION FOR ENTERPRISES
- 6.4.2 AI-AUGMENTED HUMAN-LED PENETRATION TESTING
- 6.4.3 ATTACK SURFACE INTELLIGENCE-DRIVEN PENETRATION TESTING
- 6.4.4 API AND DIGITAL ECOSYSTEM PENETRATION TESTING
- 6.5 IMPACT OF AI/GEN AI ON PENETRATION TESTING MARKET
- 6.5.1 BEST PRACTICES IN PENETRATION TESTING MARKET
- 6.5.2 CASE STUDIES OF AI IMPLEMENTATION IN PENETRATION TESTING MARKET
- 6.5.3 INTERCONNECTED ADJACENT ECOSYSTEM AND IMPACT ON MARKET PLAYERS
- 6.5.4 CLIENTS' READINESS TO ADOPT GENERATIVE AI IN PENETRATION TESTING MARKET
7 REGULATORY LANDSCAPE
- 7.1 REGIONAL REGULATIONS AND COMPLIANCE
- 7.1.1 REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
- 7.1.2 INDUSTRY STANDARDS
8 CONSUMER LANDSCAPE & BUYER BEHAVIOR
- 8.1 DECISION-MAKING PROCESS
- 8.2 BUYER STAKEHOLDERS AND BUYING EVALUATION CRITERIA
- 8.2.1 KEY STAKEHOLDERS IN BUYING PROCESS
- 8.2.2 BUYING CRITERIA
- 8.3 ADOPTION BARRIERS & INTERNAL CHALLENGES
- 8.4 UNMET NEEDS IN VARIOUS END-USE INDUSTRIES
- 8.5 MARKET PROFITABILITY
- 8.5.1 REVENUE POTENTIAL
- 8.5.2 COST DYNAMICS
- 8.5.3 MARGIN OPPORTUNITIES IN KEY APPLICATIONS
9 PENETRATION TESTING MARKET, BY TESTING TYPE
- 9.1 INTRODUCTION
- 9.1.1 TESTING TYPE: PENETRATION TESTING MARKET DRIVERS
- 9.2 BLACK BOX TESTING
- 9.2.1 EXPANDING EXTERNAL ATTACK SURFACE VALIDATION TO DRIVE MARKET
- 9.3 WHITE BOX TESTING
- 9.3.1 INCREASING DEMAND FOR DEEP CODE AND CONFIGURATION ANALYSIS TO SUPPORT MARKET GROWTH
- 9.4 GRAY BOX TESTING
- 9.4.1 GROWING ADOPTION OF BALANCED INSIDER THREAT SIMULATION TO PROPEL MARKET
10 PENETRATION TESTING MARKET, BY SERVICE TYPE
- 10.1 INTRODUCTION
- 10.1.1 SERVICE TYPE: PENETRATION TESTING MARKET DRIVERS
- 10.2 MANUAL PENETRATION TESTING
- 10.2.1 INCREASING ENTERPRISE RELIANCE ON CONTEXTUAL AND EXPLOIT-VALIDATED SECURITY ASSESSMENTS TO DRIVE MARKET
- 10.3 AUTOMATED PENETRATION TESTING
- 10.3.1 SHIFT TOWARD CONTINUOUS COMPLIANCE MONITORING TO DRIVE MARKET
11 PENETRATION TESTING MARKET, BY ATTACK SURFACE
- 11.1 INTRODUCTION
- 11.1.1 ATTACK SURFACE: PENETRATION TESTING MARKET DRIVERS
- 11.2 NETWORK SECURITY PENETRATION TESTING
- 11.2.1 INTERNAL NETWORK TESTING
- 11.2.1.1 Rising internal threat exposure and lateral movement risks to drive market
- 11.2.2 EXTERNAL NETWORK TESTING
- 11.2.2.1 Increasing exploitation of publicly accessible infrastructure to propel market
- 11.2.1 INTERNAL NETWORK TESTING
- 11.3 APPLICATION SECURITY PENETRATION TESTING
- 11.3.1 WEB APPLICATION PENETRATION TESTING
- 11.3.1.1 Process combines automated scanning with detailed manual exploitation methods
- 11.3.2 MOBILE APPLICATION PENETRATION TESTING
- 11.3.2.1 Helps identify exploitable vulnerabilities across client-side code, backend communication channels, and local data storage
- 11.3.3 API PENETRATION TESTING
- 11.3.3.1 Simulates real-world attacks against application programming interfaces
- 11.3.1 WEB APPLICATION PENETRATION TESTING
- 11.4 CLOUD SECURITY PENETRATION TESTING
- 11.4.1 ESCALATING RISKS FROM MISCONFIGURED CLOUD STORAGE AND ACCESS CONTROLS TO DRIVE MARKET
- 11.5 SOCIAL ENGINEERING SECURITY PENTESTING
- 11.5.1 MITIGATING HUMAN-LAYER AND CREDENTIAL-BASED EXPLOITATION RISKS TO DRIVE ADOPTION
- 11.6 OT/ICS SECURITY PENETRATION TESTING
- 11.6.1 DESIGNED TO IDENTIFY, VALIDATE, AND SAFELY DEMONSTRATE EXPLOITABLE WEAKNESSES ACROSS CONTROL NETWORKS
12 PENETRATION TESTING MARKET, BY ORGANIZATION SIZE
- 12.1 INTRODUCTION
- 12.1.1 ORGANIZATION SIZE: PENETRATION TESTING MARKET DRIVERS
- 12.2 LARGE ENTERPRISES
- 12.2.1 IMPLEMENT STRUCTURED, RECURRING ENTERPRISE-WIDE SECURITY VALIDATION
- 12.3 SMALL & MEDIUM-SIZED ENTERPRISES
- 12.3.1 ENHANCE EXTERNAL EXPOSURE PROTECTION THROUGH SCALABLE TESTING MODELS
13 PENETRATION TESTING MARKET, BY DEPLOYMENT MODE
- 13.1 INTRODUCTION
- 13.1.1 DEPLOYMENT TYPE: PENETRATION TESTING MARKET DRIVERS
- 13.2 CLOUD
- 13.2.1 SECURING ELASTIC CLOUD WORKLOADS AND DYNAMIC INFRASTRUCTURE ENVIRONMENTS TO DRIVE MARKET
- 13.3 ON-PREMISES
- 13.3.1 ESCALATING RISKS FROM LEGACY SYSTEMS AND INTERNAL ACCESS MISCONFIGURATIONS TO DRIVE MARKET
14 PENETRATION TESTING MARKET, BY VERTICAL
- 14.1 INTRODUCTION
- 14.1.1 VERTICAL: PENETRATION TESTING MARKET DRIVERS
- 14.2 BFSI
- 14.2.1 NEED TO SAFEGUARD DIGITAL FINANCIAL TRANSACTIONS AND API-DRIVEN BANKING SYSTEMS TO DRIVE MARKET
- 14.3 HEALTHCARE
- 14.3.1 PROTECTING CLINICAL SYSTEMS AND DIGITIZED PATIENT DATA PLATFORMS TO PROPEL MARKET
- 14.4 IT & ITES
- 14.4.1 EXPANSION OF OUTSOURCED IT AND MANAGED SERVICE ENVIRONMENTS TO SUPPORT MARKET GROWTH
- 14.5 GOVERNMENT & PUBLIC SECTOR
- 14.5.1 GROWING RANSOMWARE AND PHISHING ATTACKS ON PUBLIC SECTOR ENTITIES TO DRIVE MARKET
- 14.6 TELECOMMUNICATIONS
- 14.6.1 INCREASING THREATS TO SUBSCRIBER DATA AND TELECOM CORE NETWORKS TO PROPEL MARKET
- 14.7 RETAIL AND ECOMMERCE
- 14.7.1 PROTECTING OMNICHANNEL COMMERCE AND PAYMENT INFRASTRUCTURE TO DRIVE MARKET
- 14.8 MANUFACTURING
- 14.8.1 EXPANSION OF DIGITIZED PRODUCTION AND CONNECTED PLANT NETWORKS TO DRIVE MARKET
- 14.9 ENERGY & UTILITIES
- 14.9.1 NEED FOR SAFEGUARDING CRITICAL INFRASTRUCTURE AND GRID MODERNIZATION SYSTEMS TO DRIVE MARKET
- 14.10 OTHER VERTICALS
15 PENETRATION TESTING MARKET, BY REGION
- 15.1 INTRODUCTION
- 15.2 NORTH AMERICA
- 15.2.1 NORTH AMERICA: PENETRATION TESTING MARKET DRIVERS
- 15.2.2 US
- 15.2.2.1 Increasing losses due to cybercrime and enforcement of regulations to propel market
- 15.2.3 CANADA
- 15.2.3.1 National cyber resilience mandates and financial sector oversight accelerate structured security testing
- 15.3 EUROPE
- 15.3.1 EUROPE: PENETRATION TESTING MARKET DRIVERS
- 15.3.2 UK
- 15.3.2.1 NIS regulations and financial conduct oversight drive structured penetration testing expansion
- 15.3.3 GERMANY
- 15.3.3.1 Critical infrastructure protection laws and industrial digitization accelerate adoption of penetration testing
- 15.3.4 FRANCE
- 15.3.4.1 ANSSI cybersecurity enforcement and national resilience strategy strengthen penetration testing adoption
- 15.3.5 ITALY
- 15.3.5.1 National cybersecurity perimeter regulations advance formal security testing requirements
- 15.3.6 REST OF EUROPE
- 15.4 ASIA PACIFIC
- 15.4.1 ASIA PACIFIC: PENETRATION TESTING MARKET DRIVERS
- 15.4.2 CHINA
- 15.4.2.1 Cybersecurity law enforcement and data security regulations drive controlled penetration testing expansion
- 15.4.3 JAPAN
- 15.4.3.1 Critical infrastructure security policies and digital transformation initiatives to increase demand
- 15.4.4 INDIA
- 15.4.4.1 Rapidly increasing internet penetration to fuel market
- 15.4.5 REST OF ASIA PACIFIC
- 15.5 MIDDLE EAST & AFRICA
- 15.5.1 MIDDLE EAST & AFRICA: PENETRATION TESTING MARKET DRIVERS
- 15.5.2 MIDDLE EAST
- 15.5.2.1 GCC Countries
- 15.5.2.1.1 Kingdom of Saudi Arabia
- 15.5.2.1.1.1 Regulatory enforcement and rising cyber threat activity to accelerate market growth
- 15.5.2.1.2 UAE
- 15.5.2.1.2.1 High digital connectivity and strong cyber governance to drive market
- 15.5.2.1.3 Rest of GCC countries
- 15.5.2.1.1 Kingdom of Saudi Arabia
- 15.5.2.2 Rest of Middle East
- 15.5.2.1 GCC Countries
- 15.5.3 AFRICA
- 15.5.3.1 Rapid digital financial expansion and emerging cybersecurity regulations accelerate adoption
- 15.6 LATIN AMERICA
- 15.6.1 LATIN AMERICA: PENETRATION TESTING MARKET DRIVERS
- 15.6.2 BRAZIL
- 15.6.2.1 Expanding digital banking ecosystems to drive growth
- 15.6.3 MEXICO
- 15.6.3.1 Financial sector digitization and data protection compliance to drive adoption
- 15.6.4 REST OF LATIN AMERICA
16 COMPETITIVE LANDSCAPE
- 16.1 KEY PLAYER STRATEGIES/RIGHT TO WIN
- 16.2 REVENUE ANALYSIS
- 16.3 MARKET SHARE ANALYSIS, 2025
- 16.4 BRAND COMPARISON
- 16.5 COMPANY VALUATION AND FINANCIAL METRICS
- 16.5.1 COMPANY VALUATION
- 16.5.2 FINANCIAL METRICS USING EV/EBIDTA
- 16.6 COMPANY EVALUATION MATRIX: KEY PLAYERS, 2025
- 16.6.1 STARS
- 16.6.2 EMERGING LEADERS
- 16.6.3 PERVASIVE PLAYERS
- 16.6.4 PARTICIPANTS
- 16.6.5 COMPANY FOOTPRINT: KEY PLAYERS, 2025
- 16.6.5.1 Company footprint
- 16.6.5.2 Attack surface footprint
- 16.6.5.3 Service type footprint
- 16.6.5.4 Vertical footprint
- 16.6.5.5 Regional footprint
- 16.7 COMPANY EVALUATION MATRIX: STARTUPS/SMES, 2025
- 16.7.1 PROGRESSIVE COMPANIES
- 16.7.2 RESPONSIVE COMPANIES
- 16.7.3 DYNAMIC COMPANIES
- 16.7.4 STARTING BLOCKS
- 16.7.5 COMPETITIVE BENCHMARKING: STARTUPS/SMES, 2025
- 16.7.5.1 Detailed list of key startups/SMEs
- 16.7.5.2 Competitive benchmarking of key startups/SMEs
- 16.8 COMPETITIVE SCENARIO AND TRENDS
- 16.8.1 PRODUCT/SERVICE LAUNCHES AND ENHANCEMENTS
- 16.8.2 DEALS
17 COMPANY PROFILES
- 17.1 KEY PLAYERS
- 17.1.1 SOPHOS
- 17.1.1.1 Business overview
- 17.1.1.2 Products/Solutions/Services offered
- 17.1.1.3 Recent developments
- 17.1.1.3.1 Product/service launches & enhancements
- 17.1.1.3.2 Deals
- 17.1.1.4 MnM view
- 17.1.1.4.1 Key strengths
- 17.1.1.4.2 Strategic choices
- 17.1.1.4.3 Weaknesses and competitive threats
- 17.1.2 IBM
- 17.1.2.1 Business overview
- 17.1.2.2 Products/Solutions/Services offered
- 17.1.2.3 MnM view
- 17.1.2.3.1 Key strengths
- 17.1.2.3.2 Strategic choices
- 17.1.2.3.3 Weaknesses and competitive threats
- 17.1.3 RAPID7
- 17.1.3.1 Business overview
- 17.1.3.2 Products/Solutions/Services offered
- 17.1.3.3 Recent developments
- 17.1.3.3.1 Product/service launches
- 17.1.3.4 MnM view
- 17.1.3.4.1 Key strengths
- 17.1.3.4.2 Strategic choices
- 17.1.3.4.3 Weaknesses and competitive threats
- 17.1.4 NETSPI
- 17.1.4.1 Business overview
- 17.1.4.2 Products/Solutions/Services offered
- 17.1.4.3 Recent developments
- 17.1.4.3.1 Product launches
- 17.1.4.4 MnM view
- 17.1.4.4.1 Key strengths
- 17.1.4.4.2 Strategic choices
- 17.1.4.4.3 Weaknesses and competitive threats
- 17.1.5 PENTERA
- 17.1.5.1 Business overview
- 17.1.5.2 Products/Solutions/Services offered
- 17.1.5.3 Recent developments
- 17.1.5.3.1 Deals
- 17.1.5.4 MnM view
- 17.1.5.4.1 Key strengths
- 17.1.5.4.2 Strategic choices
- 17.1.5.4.3 Weaknesses and competitive threats
- 17.1.6 FORTRA
- 17.1.6.1 Business overview
- 17.1.6.2 Products/Solutions/Services offered
- 17.1.6.3 Recent developments
- 17.1.6.3.1 Deals
- 17.1.7 COBALT
- 17.1.7.1 Business overview
- 17.1.7.2 Products/Solutions/Services offered
- 17.1.7.3 Recent developments
- 17.1.7.3.1 Product launches
- 17.1.8 SYNACK
- 17.1.8.1 Business overview
- 17.1.8.2 Products/Solutions/Services offered
- 17.1.8.3 Recent developments
- 17.1.8.3.1 Product launches/enhancements
- 17.1.9 BISHOP FOX
- 17.1.9.1 Business overview
- 17.1.9.2 Products/Solutions/Services offered
- 17.1.10 INVICTI
- 17.1.10.1 Business overview
- 17.1.10.2 Products/Solutions/Services offered
- 17.1.10.3 Recent developments
- 17.1.10.3.1 Deals
- 17.1.11 LEVELBLUE
- 17.1.11.1 Business overview
- 17.1.11.2 Products/Solutions/Services offered
- 17.1.11.3 Recent developments
- 17.1.11.3.1 Deals
- 17.1.12 CISCO SYSTEMS
- 17.1.12.1 Business overview
- 17.1.12.2 Products/Solutions/Services offered
- 17.1.13 CROWDSTRIKE
- 17.1.13.1 Business overview
- 17.1.13.2 Products/Solutions/Services offered
- 17.1.14 FORTINET
- 17.1.14.1 Business overview
- 17.1.14.2 Products/Solutions/Services offered
- 17.1.15 CIGNITI TECHNOLOGIES
- 17.1.15.1 Business overview
- 17.1.15.2 Products/Solutions/Services offered
- 17.1.16 RAXIS
- 17.1.16.1 Business overview
- 17.1.16.2 Products/Solutions/Services offered
- 17.1.17 ASTRA SECURITY
- 17.1.18 SOFTWARE SECURED
- 17.1.19 BUGCROWD
- 17.1.20 HACKERONE
- 17.1.21 RSI SECURITY
- 17.1.22 SCIENCESOFT
- 17.1.23 PORTSWIGGER
- 17.1.24 NOWSECURE
- 17.1.25 SOFTWARE SECURED
- 17.1.26 RHINO SECURITY LABS
- 17.1.27 VUMETRIC CYBERSECURITY
- 17.1.28 NETITUDE
- 17.1.29 NETRAGARD
- 17.1.30 ZIMPERIUM
- 17.1.31 SECURITYMETRICS
- 17.1.32 COALFIRE
- 17.1.33 INDIUM SOFTWARE
- 17.1.34 TERRA SECURITY
- 17.1.35 AIKIDO
- 17.1.1 SOPHOS
18 RESEARCH METHODOLOGY
- 18.1 RESEARCH DATA
- 18.1.1 SECONDARY DATA
- 18.1.2 PRIMARY DATA
- 18.1.2.1 Breakup of primary profiles
- 18.1.2.2 Key insights from industry experts
- 18.2 DATA TRIANGULATION
- 18.3 MARKET SIZE ESTIMATION
- 18.3.1 TOP-DOWN APPROACH
- 18.3.2 BOTTOM-UP APPROACH
- 18.4 MARKET FORECAST
- 18.5 RESEARCH ASSUMPTIONS
- 18.6 RESEARCH LIMITATIONS
19 APPENDIX
- 19.1 DISCUSSION GUIDE
- 19.2 KNOWLEDGESTORE: MARKETSANDMARKETS' SUBSCRIPTION PORTAL
- 19.3 CUSTOMIZATION OPTIONS
- 19.4 RELATED REPORTS
- 19.5 AUTHOR DETAILS

