
|
시장보고서
상품코드
1993567
보안 테스트 시장 : 유형별, 네트워크 보안 테스트별, 애플리케이션 테스트 도구별 - 세계 예측(-2031년)Security Testing Market by Type (Network, Application, Device, Social Engineering), Network Security Testing (Penetration Testing, Vulnerability Scanning, Firewall), Application Testing Tool (RASP, SAST, DAST, IAST) - Global Forecast to 2031 |
||||||
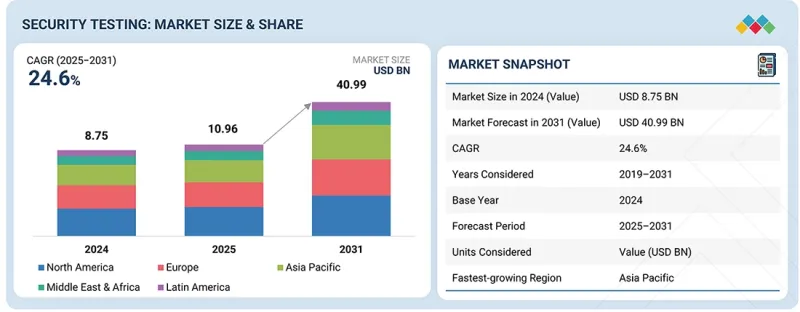
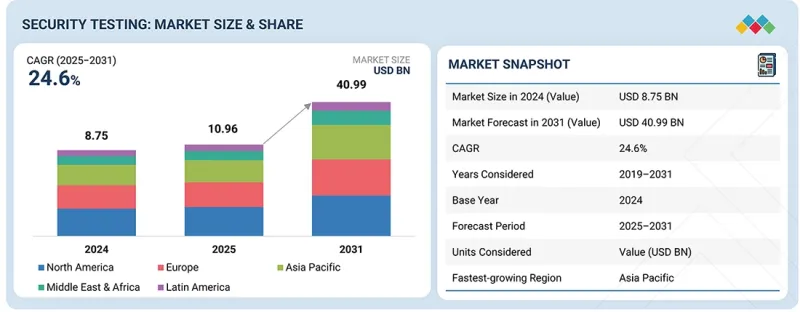
세계의 보안 테스트 시장 규모는 2025년 109억 6,000만 달러에서 2031년까지 409억 9,000만 달러에 달할 것으로 예측되며, 예측 기간 동안 CAGR로 24.6%의 성장이 전망됩니다.
| 조사 범위 | |
|---|---|
| 조사 대상 기간 | 2019-2031년 |
| 기준 연도 | 2024년 |
| 예측 기간 | 2025-2031년 |
| 단위 | 10억 달러 |
| 부문 | 보안 테스트 유형, 네트워크 보안 테스트 유형, 애플리케이션 보안 테스트 유형, 애플리케이션 보안 테스트 도구, 전개 방식, 조직 규모, 업계, 지역 |
| 대상 지역 | 북미, 유럽, 아시아태평양, 중동 및 아프리카, 라틴아메리카 |
이 시장은 웹과 모바일 애플리케이션의 급속한 보급에 의해 주도되고 있습니다. 이로 인해 외부에 노출되는 디지털 인터페이스의 수가 크게 증가하여 사이버 공격에 대한 취약성이 증가하고 있습니다. 또한, 조직은 사용자 경험을 해치지 않는 범위 내에서 잦은 업데이트와 새로운 기능을 제공해야 하는 상황에 직면해 있습니다. 릴리스 주기가 빨라짐에 따라 보안 결함이 유입될 위험이 높아지고 있으며, 비즈니스 민첩성을 유지하면서 애플리케이션의 안정성, 성능, 사용자 신뢰를 유지하기 위해서는 정기적이고 체계적인 보안 테스트가 필수적입니다.
"애플리케이션 보안 테스트 유형별로는 모바일 애플리케이션 보안 테스트 부문이 예측 기간 동안 가장 높은 CAGR을 기록할 것으로 예상됩니다."
기업이 고객 서비스, 결제, 직원 업무 지원 등 모바일 앱에 대한 의존도가 높아지면서 모바일 애플리케이션 보안 테스트가 가장 빠른 속도로 성장하고 있습니다. 모바일 애플리케이션은 다양한 기기와 OS에서 작동하면서 기밀성이 높은 개인정보와 금융 데이터를 처리하는 경우가 많으며, 이로 인해 보안 취약점에 노출될 위험이 높아집니다. Veracode에 따르면, 2025년 1월 현재 기업이 평가한 모바일 애플리케이션은 인증 및 데이터 처리 결함이 빈번하게 발견되었으며, 이는 빠른 개발 주기에서 발생한 지속적인 보안 격차를 반영하는 것으로 나타났습니다. 또한, 모바일 애플리케이션은 새로운 기능을 지원하기 위해 자주 업데이트되기 때문에 성능 및 사용자 신뢰에 영향을 미칠 수 있는 취약점이 유입될 위험이 높아집니다.
BYOD 정책의 확산과 원격근무 모델의 확산으로 기업 환경 전반에 걸쳐 모바일 위협에 대한 노출이 확대되고 있습니다. 모바일 애플리케이션을 지원하는 안전한 코딩 관행, API와의 연계, 백엔드와의 통합을 검증하기 위해서는 보안 테스트가 필수적입니다. 모바일 애플리케이션 보안 테스트는 조직이 배포 전에 취약점을 식별하고, 사용자 데이터를 보호하며, 애플리케이션의 신뢰성을 유지하는 데 도움이 됩니다. BFSI(은행, 금융, 보험), 소매, 의료, 정부 부문에서 모바일 플랫폼이 주요 디지털 채널로 자리 잡으면서 전문적인 모바일 보안 테스트에 대한 수요는 지속적으로 증가하고 있습니다.
"네트워크 보안 유형별로는 네트워크 침입 테스트 부문이 2025년 가장 큰 시장 점유율을 차지할 것으로 예측됩니다."
네트워크 침투 테스트는 실제 공격 시나리오를 시뮬레이션하고 보안 대책의 유효성을 검증할 수 있다는 점에서 가장 큰 시장 점유율을 차지하고 있습니다. 기업은 온프레미스 인프라, 클라우드 플랫폼, 원격 액세스 시스템에 걸쳐 복잡한 네트워크 환경을 운영하고 있습니다. Rapid7에 따르면, 2025년 2월 현재, 조직은 자동 스캔으로 발견할 수 없는 설정 오류나 횡방향 이동 경로와 같은 약점을 식별하기 위해 침투 테스트에 대한 의존도를 높이고 있습니다. 이러한 발견은 공격자가 네트워크의 약점을 어떻게 악용할 수 있는지를 이해하는 데 매우 중요합니다.
세계의 보안 테스트 시장에 대해 조사 분석했으며, 주요 촉진요인 및 저해요인, 제품 개발 및 혁신, 경쟁 구도 등의 정보를 전해드립니다.
자주 묻는 질문
목차
제1장 소개
제2장 주요 요약
제3장 중요한 인사이트
제4장 시장 개요
제5장 업계 동향
제6장 기술의 진보, AI에 의한 영향, 특허, 혁신, 향후 용도
제7장 규제 상황
제8장 소비자 상황과 구매 행동
제9장 보안 테스트 시장 : 보안 테스트 유형별
제10장 보안 테스트 시장 : 네트워크 보안 테스트 유형별
제11장 보안 테스트 시장 : 애플리케이션 보안 테스트 유형별
제12장 보안 테스트 시장 : 애플리케이션 보안 테스트 도구별
제13장 보안 테스트 시장 : 전개 방식별
제14장 보안 테스트 시장 : 조직 규모별
제15장 보안 테스트 시장 : 업계별
제16장 보안 테스트 시장 : 지역별
제17장 경쟁 구도
제18장 기업 개요
제19장 조사 방법
제20장 부록
KSM 26.04.15The security testing market is projected to grow from USD 10.96 billion in 2025 to USD 40.99 billion by 2031 at a Compound Annual Growth Rate (CAGR) of 24.6% during the forecast period.
| Scope of the Report | |
|---|---|
| Years Considered for the Study | 2019-2031 |
| Base Year | 2024 |
| Forecast Period | 2025-2031 |
| Units Considered | Value (USD Billion) |
| Segments | Security Testing Type, Network Security Testing Type, Application Security Testing Type, Application Security Testing Tool, Deployment Mode, Organization Size, Vertical, and Region |
| Regions covered | North America, Europe, Asia Pacific, Middle East & Africa, Latin America |
The market is driven by the rapid adoption of web and mobile applications, which has significantly increased the number of exposed digital interfaces and heightened vulnerability to cyberattacks. In addition to this, organizations are under pressure to deliver frequent updates and new features without disrupting user experience. Accelerated release cycles increase the risk of introducing security flaws, making regular and structured security testing essential to maintain application reliability, performance, and user trust while supporting business agility.
"By application security testing type, the mobile application security testing segment is expected to witness the highest CAGR during the forecast period."
Mobile application security testing is growing at the fastest rate as enterprises increasingly rely on mobile apps to deliver customer services, payments, and workforce enablement. Mobile applications often process sensitive personal and financial data while operating across diverse devices and operating systems, which increases exposure to security weaknesses. According to Veracode, in January 2025, mobile applications assessed by enterprises frequently exhibited authentication and data handling flaws, reflecting persistent security gaps introduced during rapid development cycles. Mobile applications are also updated frequently to support new features, which raises the likelihood of introducing vulnerabilities that may impact performance and user trust.
The widespread adoption of bring your own device (BYOD) policies and remote work models has expanded mobile threat exposure across enterprise environments. Security testing is required to validate secure coding practices, API interactions, and backend integrations that support mobile applications. Mobile application security testing helps organizations identify vulnerabilities before deployment, protect user data, and maintain application reliability. As mobile platforms continue to serve as primary digital channels across BFSI, retail, healthcare, and government sectors, demand for specialized mobile security testing continues to accelerate.
"By network security type, the network penetration testing segment is projected to hold the largest market share in 2025."
Network penetration testing holds the largest market share due to its ability to simulate real-world attack scenarios and validate the effectiveness of security controls. Enterprises operate complex network environments that span on-premises infrastructure, cloud platforms, and remote access systems. According to Rapid7, in February 2025, organizations increasingly relied on penetration testing to identify weaknesses that automated scans often fail to uncover, such as misconfigurations and lateral movement paths. These insights are critical for understanding how attackers could exploit network weaknesses.
Network penetration testing supports compliance requirements across regulated industries, where organizations must demonstrate that defenses are tested against realistic threats. It also plays a key role in assessing the security impact of cloud migration and hybrid work environments. Penetration testing provides actionable findings that help security teams prioritize remediation efforts and improve incident preparedness. As cyberattacks become more targeted and sophisticated, enterprises continue to view network penetration testing as an essential component of proactive risk management and network resilience strategies.
By application security testing tool, the static application security testing (SAST) segment is expected to lead the market during the forecast period.
Static application security testing remains a core tool within application security programs as organizations seek to identify vulnerabilities early in the software development lifecycle. SAST analyzes source code to detect security weaknesses before applications are deployed, reducing remediation costs and development delays. According to Checkmarx, in April 2025, development teams increasingly embedded SAST into continuous integration pipelines to support faster releases while maintaining security standards. Early detection of flaws helps prevent vulnerabilities from reaching production environments.
SAST is widely adopted because it integrates directly into developer workflows and supports secure coding practices across large application portfolios. It is particularly valuable for identifying common coding errors, insecure functions, and compliance-related issues. As enterprises adopt agile and DevSecOps models, SAST enables consistent security testing without slowing development velocity. Its ability to scale across complex and distributed development environments reinforces its continued growth among application security testing tools.
Breakdown of Primaries
The study draws insights from a range of industry experts, including component suppliers, Tier 1 companies, and OEMs. The break-up of the primaries is as follows:
- By Company Type: Tier 1 - 20%, Tier 2 - 32%, and Tier 3 - 48%
- By Designation: C-level - 40%, Managerial Level, and Others - 60%
- By Region: North America - 40%, Europe - 25%, Asia Pacific - 20%, Middle East & Africa - 10%, Latin America - 5%
Major vendors in the security testing market include IBM (US), HCLTech (India), Black Duck (Synopsys) (US), OpenText (Canada), Cigniti Technologies (Coforge) (India), Qualitest (UK), Intertek (UK), DXC Technology (US), elnfochips (US), Checkmarx (US), HackerOne (US), Invicti (US), DataArt (US), Cobalt (US), LevelBlue (Trustwave) (US), Contrast Security (US), Veracode (US), Qualys (US), OffSec (US), NCC Group (UK), GitHub (US), Bugcrowd (US), Applause (US), Rapid7 (US), Parasoft (US), Breachlock (US), ImmuniWeb (Switzerland), Pentest People (UK), SafeAeon (US), REDTEAM.PL (Poland), Pentera (US), Qualizeal (US), Astra Security (US), NowSecure (US), and Fluid Attacks (US).
The study includes an in-depth competitive analysis of the key players in the security testing market, their company profiles, recent developments, and key market strategies.
Research Coverage
The report segments the security testing market and forecasts its size based on security testing type (network security testing, application security testing, device security testing, and social engineering security testing), network security testing type (network penetration testing, vulnerability scanning, Wi-Fi/wireless security testing, firewall security testing, network configuration auditing), application security testing type (mobile application security testing, web application security testing, api security testing, secure code review), application security testing tools (Runtime Application Self-Protection (RASP), Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), Interactive Application Security Testing (IAST)), deployment mode (on-premises and cloud), organization size (large enterprises and SMEs), and vertical (BFSI, healthcare, government, IT & ITeS, telecommunications, manufacturing, retail & e-commerce, education, energy & utilities, and others).
The study also includes an in-depth competitive analysis of the market's key players, their company profiles, key observations related to product and business offerings, recent developments, and key market strategies.
Key Benefits of Buying the Report
The report will help market leaders/new entrants with information on the closest approximations of revenue numbers for the overall security testing market and its subsegments. This report will help stakeholders understand the competitive landscape and gain valuable insights to better position their businesses and plan suitable go-to-market strategies. The report also helps stakeholders understand the market pulse and provides information on key market drivers, restraints, challenges, and opportunities.
The report provides insights into the following pointers:
- Analysis of key drivers (Increased sophistication and variety in cyberattacks fueling demand for security testing, Rapid adoption of web and mobile applications vulnerable to cyberattack, Stringent government regulations to develop cybersecurity standards for data protection, Need to ensure seamless user experience with accelerated release cycles, Increasing reliance on third-party and open-source components), restraints (High false-positive rates from automated testing tools), opportunities (Emergence of technologies, such as AI and ML, in security testing, Increased adoption of cloud-based security testing, Integration of DevSecOps in software security testing, Growth of Security Testing as a Service (STaaS)), and challenges (Lack of skilled cybersecurity professionals, Fragmentation of security testing tools and platforms, Higher costs involved in executing security tests)
- Product Development/Innovation: Detailed insights on upcoming technologies, research & development activities, and product & service launches in the security testing market
- Market Development: Comprehensive information about lucrative markets - the report analyzes the security testing market across varied regions
- Market Diversification: Exhaustive information about new products & services, untapped geographies, recent developments, and investments in the security testing market
- Competitive Assessment: In-depth assessment of market shares, growth strategies, and service offerings of leading players in the security testing market, including IBM (US), Intertek (UK), Cigniti Technologies (Coforge) (US), OpenText (Canada), and Qualitest (UK)
TABLE OF CONTENTS
1 INTRODUCTION
- 1.1 STUDY OBJECTIVES
- 1.2 MARKET DEFINITION
- 1.3 STUDY SCOPE AND SEGMENTATION
- 1.3.1 MARKET SEGMENTATION
- 1.3.2 INCLUSIONS AND EXCLUSIONS
- 1.3.3 YEARS CONSIDERED
- 1.4 CURRENCY CONSIDERED
- 1.5 STAKEHOLDERS
- 1.6 SUMMARY OF CHANGES
2 EXECUTIVE SUMMARY
- 2.1 MARKET HIGHLIGHTS AND KEY INSIGHTS
- 2.2 KEY MARKET PARTICIPANTS: MAPPING OF STRATEGIC DEVELOPMENTS
- 2.3 DISRUPTIVE TRENDS SHAPING MARKET
- 2.4 HIGH-GROWTH SEGMENTS & EMERGING FRONTIERS
- 2.5 SNAPSHOT: GLOBAL MARKET SIZE, GROWTH RATE, AND FORECAST
3 PREMIUM INSIGHTS
- 3.1 ATTRACTIVE OPPORTUNITIES FOR PLAYERS IN SECURITY TESTING MARKET
- 3.2 SECURITY TESTING MARKET, BY SECURITY TESTING TYPE
- 3.3 SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE
- 3.4 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE
- 3.5 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOLS
- 3.6 SECURITY TESTING MARKET, BY VERTICAL
- 3.7 SECURITY TESTING MARKET, BY REGION
4 MARKET OVERVIEW
- 4.1 INTRODUCTION
- 4.2 MARKET DYNAMICS
- 4.2.1 DRIVERS
- 4.2.1.1 Increased sophistication and variety in cyberattacks fueling demand for security testing
- 4.2.1.2 Rapid adoption of web and mobile applications vulnerable to cyberattack
- 4.2.1.3 Stringent government regulations to develop cybersecurity standards for data protection
- 4.2.1.4 Need to ensure seamless user experience with accelerated release cycles
- 4.2.1.5 Increasing reliance on third-party and open-source components
- 4.2.2 RESTRAINTS
- 4.2.2.1 High false-positive rates from automated testing tools
- 4.2.3 OPPORTUNITIES
- 4.2.3.1 Emergence of technologies, such as AI and ML, in security testing
- 4.2.3.2 Increased adoption of cloud-based security testing
- 4.2.3.3 Integration of DevSecOps in software security testing
- 4.2.3.4 Growth of Security Testing-as-a-Service (STaaS)
- 4.2.4 CHALLENGES
- 4.2.4.1 Lack of skilled cybersecurity professionals
- 4.2.4.2 Fragmentation of security testing tools and platforms
- 4.2.4.3 Higher costs involved in executing security tests
- 4.2.1 DRIVERS
- 4.3 UNMET NEEDS AND WHITE SPACES
- 4.4 INTERCONNECTED MARKETS AND CROSS-SECTOR OPPORTUNITIES
- 4.4.1 INTERCONNECTED MARKETS
- 4.4.2 CROSS-SECTOR OPPORTUNITIES
- 4.5 STRATEGIC MOVES BY TIER -1/2/3 PLAYERS
- 4.5.1 CROSS-TIER STRATEGIC PATTERNS
- 4.5.2 STRATEGIC TRENDS
- 4.5.2.1 Adoption of DevSecOps and shift-left security
- 4.5.2.2 AI- and ML-driven security testing
- 4.5.2.3 Growth of cloud-native and continuous security testing
5 INDUSTRY TRENDS
- 5.1 PORTER'S FIVE FORCES ANALYSIS
- 5.1.1 THREAT OF NEW ENTRANTS
- 5.1.2 THREAT OF SUBSTITUTES
- 5.1.3 BARGAINING POWER OF SUPPLIERS
- 5.1.4 BARGAINING POWER OF BUYERS
- 5.1.5 INTENSITY OF COMPETITIVE RIVALRY
- 5.2 MACROECONOMIC INDICATORS
- 5.2.1 INTRODUCTION
- 5.2.2 GDP TRENDS AND FORECAST
- 5.2.3 TRENDS IN GLOBAL ICT INDUSTRY
- 5.2.4 TRENDS IN GLOBAL CYBERSECURITY INDUSTRY
- 5.3 VALUE CHAIN ANALYSIS
- 5.3.1 SECURITY TESTING TOOLS AND SERVICE PROVIDERS
- 5.3.2 TECHNOLOGY PROVIDERS
- 5.3.3 CONSULTANTS & INTEGRATORS
- 5.3.4 REGULATORY BODIES & STANDARDS
- 5.3.5 VARS/DISTRIBUTORS/RESELLERS
- 5.3.6 END USERS
- 5.4 ECOSYSTEM
- 5.5 PRICING ANALYSIS
- 5.5.1 AVERAGE SELLING PRICE TREND OF KEY PLAYERS, BY TESTING TYPE
- 5.5.2 INDICATIVE PRICING ANALYSIS, BY VENDOR
- 5.6 KEY CONFERENCES AND EVENTS IN 2026
- 5.7 TRENDS AND DISRUPTIONS IMPACTING CUSTOMER BUSINESS
- 5.8 INVESTMENT AND FUNDING SCENARIO
- 5.9 CASE STUDY ANALYSIS
- 5.9.1 SIEMENS HEALTHINEERS ENHANCED SECURITY OF APPLICATION DEVELOPMENT WITH CHECKMARX'S STATIC CODE ANALYSIS
- 5.9.2 THALES ALENIA SPACE BOOSTED CODE QUALITY AND SECURITY USING SYNOPSYS COVERITY AND BLACK DUCK
- 5.9.3 NORTHBRIDGE FINANCIAL IMPROVED API TESTING EFFICIENCY AND COVERAGE USING PARASOFT TOOLS
- 5.9.4 COHESION ENHANCED MOBILE APP SECURITY WITH NOWSECURE PLATFORM FOR SMART BUILDING SOLUTIONS
- 5.9.5 BUGCROWD HELPED RAPYD ELEVATE SECURITY WITH PENETRATION TESTING-AS-A-SERVICE AND BUG BOUNTY PROGRAMS
- 5.10 IMPACT OF 2025 US TARIFF - SECURITY TESTING MARKET
- 5.10.1 INTRODUCTION
- 5.10.2 KEY TARIFF RATES
- 5.10.3 PRICE IMPACT ANALYSIS
- 5.10.4 IMPACT ON COUNTRY/REGION
- 5.10.4.1 North America
- 5.10.4.2 Europe
- 5.10.4.3 Asia Pacific
- 5.10.5 IMPACT ON END-USE INDUSTRIES
6 TECHNOLOGICAL ADVANCEMENTS, AI-DRIVEN IMPACT, PATENTS, INNOVATIONS, AND FUTURE APPLICATIONS
- 6.1 TECHNOLOGY ANALYSIS
- 6.1.1 KEY EMERGING TECHNOLOGIES
- 6.1.1.1 Static Application Security Testing (SAST)
- 6.1.1.2 Dynamic Application Security Testing (DAST)
- 6.1.2 COMPLEMENTARY TECHNOLOGIES
- 6.1.2.1 Threat intelligence
- 6.1.2.2 DevSecOps
- 6.1.3 ADJACENT TECHNOLOGIES
- 6.1.3.1 Artificial Intelligence (AI) and Machine Learning (ML)
- 6.1.3.2 Blockchain
- 6.1.1 KEY EMERGING TECHNOLOGIES
- 6.2 TECHNOLOGY ROADMAP
- 6.2.1 SHORT-TERM (2026-2027) | FOUNDATION & EARLY COMMERCIALIZATION
- 6.2.2 MID-TERM (2027-2030) SCALING, INTELLIGENCE & ECOSYSTEM EXPANSION
- 6.2.3 LONG-TERM (2030-2035+) | AUTONOMOUS, REAL-TIME & ADAPTIVE SECURITY
- 6.3 PATENT ANALYSIS
- 6.4 FUTURE APPLICATIONS
- 6.4.1 AUTONOMOUS & AI-DRIVEN SECURITY TESTING PLATFORMS
- 6.4.2 DATA-DRIVEN SECURITY ANALYTICS & PREDICTIVE RISK INSIGHTS
- 6.4.3 ADVANCED THREAT SIMULATION & ATTACK EMULATION
- 6.4.4 AI-DRIVEN ADAPTIVE SECURITY TESTING & RISK PRIORITIZATION
- 6.4.5 CONTINUOUS SECURITY VALIDATION & DEVSECOPS-INTEGRATED TESTING
- 6.5 IMPACT OF AI/GEN AI ON SECURITY TESTING MARKET
- 6.5.1 BEST PRACTICES IN SECURITY TESTING MARKET
- 6.5.2 CASE STUDIES OF AI IMPLEMENTATION IN SECURITY TESTING MARKET
- 6.5.3 INTERCONNECTED ADJACENT ECOSYSTEM AND IMPACT ON MARKET PLAYERS
- 6.5.4 CLIENTS' READINESS TO ADOPT GENERATIVE AI IN SECURITY TESTING MARKET
- 6.6 SUCCESS STORIES AND REAL-WORLD APPLICATIONS
- 6.6.1 CHECKMARX: SECURE SOFTWARE DEVELOPMENT TRANSFORMATION FOR GLOBAL ENTERPRISE
- 6.6.2 RAPID7: CLOUD-NATIVE VULNERABILITY MANAGEMENT FOR GLOBAL ENTERPRISE
7 REGULATORY LANDSCAPE
- 7.1 REGIONAL REGULATIONS AND COMPLIANCE
- 7.1.1 REGULATORY BODIES, GOVERNMENT AGENCIES, AND OTHER ORGANIZATIONS
- 7.1.2 INDUSTRY STANDARDS
8 CONSUMER LANDSCAPE & BUYER BEHAVIOR
- 8.1 DECISION-MAKING PROCESS
- 8.2 BUYER STAKEHOLDERS AND BUYING EVALUATION CRITERIA
- 8.2.1 KEY STAKEHOLDERS IN BUYING PROCESS
- 8.2.2 BUYING CRITERIA
- 8.3 ADOPTION BARRIERS & INTERNAL CHALLENGES
- 8.4 UNMET NEEDS IN VARIOUS END-USE INDUSTRIES
- 8.5 MARKET PROFITABILITY
- 8.5.1 REVENUE POTENTIAL
- 8.5.2 COST DYNAMICS
- 8.5.3 MARGIN OPPORTUNITIES IN KEY APPLICATIONS
9 SECURITY TESTING MARKET, BY SECURITY TESTING TYPE
- 9.1 INTRODUCTION
- 9.1.1 SECURITY TESTING TYPE: SECURITY TESTING MARKET DRIVERS
- 9.2 NETWORK SECURITY TESTING
- 9.2.1 RAPID GROWTH OF CYBERATTACKS AND NEED TO ADDRESS NETWORK SECURITY ISSUES AND MINIMIZE DATA LOSS TO PROPEL MARKET
- 9.3 APPLICATION SECURITY TESTING
- 9.3.1 NEED TO IDENTIFY VULNERABILITIES, THREATS, AND RISKS IN INTERNAL AND EXTERNAL APPLICATIONS TO FUEL MARKET GROWTH
- 9.4 DEVICE SECURITY TESTING
- 9.4.1 ADVANCEMENTS IN DEVICE SECURITY TESTING WITH POST-QUANTUM CRYPTOGRAPHY SOLUTIONS TO BOOST MARKET GROWTH
- 9.5 SOCIAL ENGINEERING TESTING
- 9.5.1 SOCIAL ENGINEERING TESTING TO MITIGATE RISKS WITH ENHANCED PENETRATION TESTING
10 SECURITY TESTING MARKET, BY NETWORK SECURITY TESTING TYPE
- 10.1 INTRODUCTION
- 10.1.1 NETWORK SECURITY TESTING TYPE: SECURITY TESTING MARKET DRIVERS
- 10.2 NETWORK PENETRATION TESTING
- 10.2.1 NETWORK PENETRATION TESTING TO HELP ETHICAL HACKERS SIMULATE CYBERATTACKS TO UNCOVER VULNERABILITIES
- 10.3 VULNERABILITY SCANNING
- 10.3.1 NETWORK VULNERABILITY SCANNING SOLUTIONS TO IDENTIFY AND MITIGATE POTENTIAL THREATS
- 10.4 WI-FI/WIRELESS SECURITY TESTING
- 10.4.1 NEED TO IDENTIFY VULNERABILITIES IN WIRELESS NETWORKS AND ENSURE PROTECTION OF SENSITIVE DATA AND SYSTEMS TO BOLSTER MARKET GROWTH
- 10.5 FIREWALL SECURITY TESTING
- 10.5.1 FIREWALL SECURITY TESTING TO EVALUATE EFFECTIVENESS OF FIREWALLS IN PROTECTING NETWORKS FROM UNAUTHORIZED ACCESS AND CYBER THREATS
- 10.6 NETWORK CONFIGURATION AUDITING
- 10.6.1 NETWORK CONFIGURATION AUDITING TO SCAN NETWORK INFRASTRUCTURE, CHECK FOR COMPLIANCE WITH SECURITY POLICIES, AND IDENTIFY DEVICES WITH OUTDATED FIRMWARE OR INSECURE CONFIGURATIONS
11 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TYPE
- 11.1 INTRODUCTION
- 11.1.1 APPLICATION SECURITY TESTING TYPE: SECURITY TESTING MARKET DRIVERS
- 11.2 MOBILE APPLICATION SECURITY TESTING
- 11.2.1 MOBILE APPLICATION SECURITY TESTING TO PROTECT SENSITIVE DATA, HELP ORGANIZATIONS ADHERE TO REGULATIONS, AND ENHANCE SECURITY POSTURE
- 11.3 WEB APPLICATION SECURITY TESTING
- 11.3.1 WEB APPLICATION SECURITY TESTING TO HELP PREVENT DATA BREACHES, ENSURE COMPLIANCE WITH INDUSTRY STANDARDS, AND MAINTAIN USER TRUST
- 11.4 API SECURITY TESTING
- 11.4.1 API SECURITY TESTING TO VALIDATE API ENDPOINTS TO DETECT VULNERABILITIES THAT ATTACKERS MIGHT EXPLOIT AND ENSURE SAFE INTEGRATION WITH DEVELOPMENT PROCESSES
- 11.5 SECURE CODE REVIEW
- 11.5.1 SECURE CODE REVIEW TO HELP DEVELOPERS ADDRESS ISSUES EARLY BY ANALYZING CODE FOR POTENTIAL SECURITY FLAWS AND PREVENTING FUTURE BREACHES AND ATTACKS
12 SECURITY TESTING MARKET, BY APPLICATION SECURITY TESTING TOOL
- 12.1 INTRODUCTION
- 12.1.1 APPLICATION SECURITY TESTING TOOL: SECURITY TESTING MARKET DRIVERS
- 12.2 RUNTIME APPLICATION SELF-PROTECTION (RASP)
- 12.2.1 RASP TO PROTECT APPLICATIONS IN REAL-TIME BY DETECTING AND BLOCKING ATTACKS
- 12.3 STATIC APPLICATION SECURITY TESTING (SAST)
- 12.3.1 NEXT-GEN SAST TOOLS TO ENHANCE SPEED AND ACCURACY AND HELP IDENTIFY AND FIX SECURITY FLAWS EARLY
- 12.4 DYNAMIC APPLICATION SECURITY TESTING (DAST)
- 12.4.1 DAST TOOLS TO EVALUATE WEB APPLICATIONS WHILE RUNNING AND SIMULATE REAL-WORLD ATTACKS TO IDENTIFY VULNERABILITIES
- 12.5 INTERACTIVE APPLICATION SECURITY TESTING (IAST)
- 12.5.1 INTERACTIVE APPLICATION SECURITY TESTING (IAST) TO COMBINE STATIC AND DYNAMIC TESTING ELEMENTS TO UNCOVER WEB APPLICATION VULNERABILITIES DURING RUNTIME INTEGRATION
13 SECURITY TESTING MARKET, BY DEPLOYMENT MODE
- 13.1 INTRODUCTION
- 13.1.1 DEPLOYMENT MODE: SECURITY TESTING MARKET DRIVERS
- 13.2 ON-PREMISES
- 13.2.1 ON-PREMISE DEPLOYMENT IS PARTICULARLY IMPORTANT FOR LEGACY SYSTEMS AND OPERATIONAL TECHNOLOGY ENVIRONMENTS WHERE EXTERNAL CONNECTIVITY IS LIMITED
- 13.3 CLOUD
- 13.3.1 CONTINUOUS VISIBILITY AND VULNERABILITY MANAGEMENT ACROSS DISTRIBUTED ENVIRONMENTS TO DRIVE MARKET GROWTH
14 SECURITY TESTING MARKET, BY ORGANIZATION SIZE
- 14.1 INTRODUCTION
- 14.1.1 ORGANIZATION SIZE: SECURITY TESTING MARKET DRIVERS
- 14.2 LARGE ENTERPRISES
- 14.2.1 TREND OF DIGITALIZATION AND SECURITY TESTING, GROWING CONNECTIVITY OF BANDWIDTHS, AND MOBILITY TRENDS IN LARGE ENTERPRISES TO DRIVE MARKET
- 14.3 SMALL AND MEDIUM-SIZED ENTERPRISES
- 14.3.1 COMPLEX IT ENVIRONMENTS AND NEED TO COMPLY WITH STRINGENT DATA PROTECTION REGULATIONS TO PROPEL MARKET
15 SECURITY TESTING MARKET, BY VERTICAL
- 15.1 INTRODUCTION
- 15.1.1 VERTICAL: SECURITY TESTING MARKET DRIVERS
- 15.2 BANKING, FINANCIAL SERVICES, AND INSURANCE
- 15.2.1 RELIANCE ON DIGITAL PLATFORMS FOR SMART BANKING, INTERNET BANKING, AND MOBILE TRANSACTIONS INCREASING CYBERATTACKS TO FOSTER MARKET GROWTH
- 15.3 HEALTHCARE
- 15.3.1 CRITICAL NATURE OF OPERATIONS AND SENSITIVE NATURE OF PATIENT DATA TO DRIVE DEMAND FOR SECURITY TESTING
- 15.4 GOVERNMENT & DEFENSE
- 15.4.1 ESCALATING CYBER THREATS AND EVOLVING REGULATORY REQUIREMENTS TO BOOST DEMAND FOR SECURITY TESTING SOLUTIONS
- 15.5 IT & ITES
- 15.5.1 CONTINUOUS DEVELOPMENT OF NEW SOLUTIONS AND EXTENSIVE USE OF WEB AND MOBILE APPLICATIONS TO RISE DEMAND FOR SECURITY TESTING SOLUTIONS
- 15.6 TELECOMMUNICATIONS
- 15.6.1 NEED TO PROTECT AGAINST EVOLVING THREATS, COMPLY WITH REGULATORY STANDARDS, AND ENSURE RELIABILITY OF SERVICES TO BOOST MARKET GROWTH
- 15.7 MANUFACTURING
- 15.7.1 SECURITY TESTING TO HELP ADHERE TO COMPLIANCE REQUIREMENTS, PROTECT AGAINST POTENTIAL DATA BREACHES, AND ENSURE OVERALL SECURITY OF MANUFACTURING OPERATIONS
- 15.8 RETAIL & ECOMMERCE
- 15.8.1 DIGITAL TRANSFORMATION IN RETAIL AND HIGH-VALUE TRANSACTIONS TO ACCELERATE MARKET GROWTH
- 15.9 EDUCATION
- 15.9.1 SURGE IN VULNERABILITIES IN ELEARNING SECTOR AND SHIFT TOWARD DIGITAL TECHNOLOGIES FOR EDUCATIONAL DATA TO PROPEL MARKET
- 15.10 ENERGY & UTILITIES
- 15.10.1 RAPID INCORPORATION OF DIGITAL TECHNOLOGIES INCREASING EXPOSURE TO CYBERATTACKS TO DRIVE MARKET
- 15.11 OTHER VERTICALS
16 SECURITY TESTING MARKET, BY REGION
- 16.1 INTRODUCTION
- 16.2 NORTH AMERICA
- 16.2.1 NORTH AMERICA: SECURITY TESTING MARKET DRIVERS
- 16.2.2 US
- 16.2.2.1 Focus on strategic developments and rising incidents of cyber threats to drive market
- 16.2.3 CANADA
- 16.2.3.1 Emphasis on regulatory frameworks and critical infrastructure security to drive market
- 16.3 EUROPE
- 16.3.1 EUROPE: SECURITY TESTING MARKET DRIVERS
- 16.3.2 UK
- 16.3.2.1 Strategic advancement in security testing through AI collaboration to boost market growth
- 16.3.3 GERMANY
- 16.3.3.1 Rapid digital transformation and surge in cyber threats to boost demand for security testing
- 16.3.4 FRANCE
- 16.3.4.1 Expanding cybersecurity landscape to boost demand for security testing solutions
- 16.3.5 ITALY
- 16.3.5.1 Rise in sophisticated cyberattacks and demand for cybersecurity in automotive & industrial sectors to propel market
- 16.3.6 REST OF EUROPE
- 16.4 ASIA PACIFIC
- 16.4.1 ASIA PACIFIC: SECURITY TESTING MARKET DRIVERS
- 16.4.2 CHINA
- 16.4.2.1 Rapid digital expansion and increasing cyber risks to drive security testing demand
- 16.4.3 JAPAN
- 16.4.3.1 Increasing cyber incidents and digital infrastructure expansion to drive security testing demand
- 16.4.4 INDIA
- 16.4.4.1 Advancements in India's security testing frameworks and implementation of new regulations to propel market
- 16.4.5 REST OF ASIA PACIFIC
- 16.5 MIDDLE EAST & AFRICA
- 16.5.1 MIDDLE EAST & AFRICA: SECURITY TESTING MARKET DRIVERS
- 16.5.2 GCC
- 16.5.2.1 Implementation of 'Vision for Regional Security' to accelerate market growth
- 16.5.2.2 KSA
- 16.5.2.2.1 Growing digital transformation and rising instances of cyber threats to drive market
- 16.5.2.3 UAE
- 16.5.2.3.1 Increasing smart infrastructure expansion to drive security testing demand
- 16.5.2.4 Rest of GCC countries
- 16.5.3 SOUTH AFRICA
- 16.5.3.1 Growing prevalence of phishing attacks, social engineering scams, and phishing scams to propel market
- 16.5.4 REST OF MIDDLE EAST & AFRICA
- 16.6 LATIN AMERICA
- 16.6.1 LATIN AMERICA: SECURITY TESTING MARKET DRIVERS
- 16.6.2 BRAZIL
- 16.6.2.1 Rise in digital adoption to foster market growth
- 16.6.3 MEXICO
- 16.6.3.1 State-driven cyber-espionage and hacktivism and vulnerability of government organizations to drive market growth
- 16.6.4 REST OF LATIN AMERICA
17 COMPETITIVE LANDSCAPE
- 17.1 KEY PLAYER STRATEGIES/RIGHT TO WIN, 2024-2026
- 17.2 REVENUE ANALYSIS, 2020-2024
- 17.3 MARKET SHARE ANALYSIS, 2025
- 17.4 BRAND COMPARISON
- 17.5 COMPANY EVALUATION MATRIX: KEY PLAYERS, 2025
- 17.5.1 STARS
- 17.5.2 EMERGING LEADERS
- 17.5.3 PERVASIVE PLAYERS
- 17.5.4 PARTICIPANTS
- 17.5.5 COMPANY FOOTPRINT: KEY PLAYERS, 2025
- 17.5.5.1 Company footprint
- 17.5.5.2 Security testing type footprint
- 17.5.5.3 Deployment mode footprint
- 17.5.5.4 Vertical footprint
- 17.5.5.5 Regional footprint
- 17.6 COMPANY EVALUATION MATRIX: STARTUPS/SMES, 2025
- 17.6.1 PROGRESSIVE COMPANIES
- 17.6.2 RESPONSIVE COMPANIES
- 17.6.3 DYNAMIC COMPANIES
- 17.6.4 STARTING BLOCKS
- 17.6.5 COMPETITIVE BENCHMARKING: STARTUPS/SMES, 2025
- 17.6.5.1 Key startups/SMEs
- 17.6.5.2 Competitive benchmarking of key startups/SMEs
- 17.7 COMPANY VALUATION AND FINANCIAL METRICS
- 17.7.1 COMPANY VALUATION
- 17.7.2 FINANCIAL METRICS USING EV/EBIDTA
- 17.8 COMPETITIVE SCENARIO AND TRENDS
- 17.8.1 PRODUCT LAUNCHES AND ENHANCEMENTS
- 17.8.2 DEALS
18 COMPANY PROFILES
- 18.1 KEY PLAYERS
- 18.1.1 IBM
- 18.1.1.1 Business overview
- 18.1.1.2 Products/Solutions/Services offered
- 18.1.1.3 Recent developments
- 18.1.1.3.1 Deals
- 18.1.1.4 MnM view
- 18.1.1.4.1 Right to win
- 18.1.1.4.2 Strategic choices
- 18.1.1.4.3 Weaknesses and competitive threats
- 18.1.2 OPENTEXT
- 18.1.2.1 Business overview
- 18.1.2.2 Products/Solutions/Services offered
- 18.1.2.3 Recent developments
- 18.1.2.3.1 Product launches
- 18.1.2.4 MnM view
- 18.1.2.4.1 Right to win
- 18.1.2.4.2 Strategic choices
- 18.1.2.4.3 Weaknesses and competitive threats
- 18.1.3 CIGNITI TECHNOLOGIES
- 18.1.3.1 Business overview
- 18.1.3.2 Products/Solutions/Services offered
- 18.1.3.3 MnM view
- 18.1.3.3.1 Right to win
- 18.1.3.3.2 Strategic choices
- 18.1.3.3.3 Weaknesses and competitive threats
- 18.1.4 INTERTEK
- 18.1.4.1 Business overview
- 18.1.4.2 Products/Solutions/Services offered
- 18.1.4.3 Recent developments
- 18.1.4.3.1 Product launches
- 18.1.4.4 MnM view
- 18.1.4.4.1 Right to win
- 18.1.4.4.2 Strategic choices
- 18.1.4.4.3 Weaknesses and competitive threats
- 18.1.5 QUALITEST
- 18.1.5.1 Business overview
- 18.1.5.2 Products/Solutions/Services offered
- 18.1.5.3 MnM view
- 18.1.5.3.1 Right to win
- 18.1.5.3.2 Strategic choices
- 18.1.5.3.3 Weaknesses and competitive threats
- 18.1.6 BLACK DUCK
- 18.1.6.1 Business overview
- 18.1.6.2 Products/Solutions/Services offered
- 18.1.7 HCLSOFTWARE
- 18.1.7.1 Business overview
- 18.1.7.2 Products/Solutions/Services offered
- 18.1.7.3 Recent developments
- 18.1.7.3.1 Deals
- 18.1.8 LEVELBLUE
- 18.1.8.1 Business overview
- 18.1.8.2 Products/Solutions/Services offered
- 18.1.8.3 Recent developments
- 18.1.8.3.1 Deals
- 18.1.9 DXC TECHNOLOGY
- 18.1.9.1 Business overview
- 18.1.9.2 Products/Solutions/Services offered
- 18.1.9.3 Recent developments
- 18.1.9.3.1 Deals
- 18.1.10 EINFOCHIPS
- 18.1.10.1 Business overview
- 18.1.10.2 Products/Solutions/Services offered
- 18.1.11 CHECKMARX
- 18.1.11.1 Business overview
- 18.1.11.2 Products/Solutions/Services offered
- 18.1.11.3 Recent developments
- 18.1.11.3.1 Product launches
- 18.1.11.3.2 Deals
- 18.1.12 HACKERONE
- 18.1.12.1 Business overview
- 18.1.12.2 Products/Solutions/Services offered
- 18.1.12.3 Recent developments
- 18.1.12.3.1 Product launches
- 18.1.12.3.2 Deals
- 18.1.13 INVICTI
- 18.1.13.1 Business overview
- 18.1.13.2 Products/Solutions/Services offered
- 18.1.13.3 Recent developments
- 18.1.13.3.1 Product launches
- 18.1.13.3.2 Deals
- 18.1.14 DATAART
- 18.1.14.1 Business overview
- 18.1.14.2 Products/Solutions/Services offered
- 18.1.15 COBALT
- 18.1.15.1 Business overview
- 18.1.15.2 Products/Solutions/Services offered
- 18.1.15.3 Recent developments
- 18.1.15.3.1 Product launches
- 18.1.15.3.2 Deals
- 18.1.16 PENTERA
- 18.1.17 QUALIZEAL
- 18.1.18 NOWSECURE
- 18.1.19 FLUID ATTACKS
- 18.1.20 ASTRA SECURITY
- 18.1.1 IBM
- 18.2 OTHER KEY PLAYERS
- 18.2.1 CONTRAST SECURITY
- 18.2.2 VERACODE
- 18.2.3 QUALYS
- 18.2.4 OFFSEC
- 18.2.5 NCC GROUP
- 18.2.6 GITHUB
- 18.2.7 BUGCROWD
- 18.2.8 APPLAUSE
- 18.2.9 RAPID7
- 18.2.10 PARASOFT
- 18.2.11 BREACHLOCK
- 18.2.12 IMMUNIWEB
- 18.2.13 PENTEST PEOPLE
- 18.2.14 SAFEAEON
- 18.2.15 REDTEAM.PL
19 RESEARCH METHODOLOGY
- 19.1 RESEARCH DATA
- 19.1.1 SECONDARY DATA
- 19.1.2 PRIMARY DATA
- 19.1.2.1 Breakdown of primary profiles
- 19.1.2.2 Key industry insights
- 19.2 DATA TRIANGULATION
- 19.3 MARKET SIZE ESTIMATION
- 19.3.1 TOP-DOWN APPROACH
- 19.3.2 BOTTOM-UP APPROACH
- 19.4 MARKET FORECAST
- 19.5 RESEARCH ASSUMPTIONS
- 19.6 RESEARCH LIMITATIONS
20 APPENDIX
- 20.1 DISCUSSION GUIDE
- 20.2 KNOWLEDGESTORE: MARKETSANDMARKETS' SUBSCRIPTION PORTAL
- 20.3 CUSTOMIZATION OPTIONS
- 20.4 RELATED REPORTS
- 20.5 AUTHOR DETAILS

